Understanding the Critical Role of a VPN in Modern Digital Life
In an era where online risks are increasing, protecting your personal information has never been more crucial. A VPN scrambles your online activity, ensuring that malicious actors, ISPs, and third parties cannot monitor your browsing habits. Whether you’re accessing public Wi-Fi at a hotel or managing sensitive documents, a VPN acts as an invisible barrier against security leaks.
People ignore the dangers of unprotected hotspots, putting at risk their credit card numbers, account details, and communication logs. By routing your connection through remote servers, a 快连 conceals your online identity and geolocation, making it nearly unfeasible for tracking agencies to profile you.
Selecting the Ideal VPN for Your Gadget: A Comprehensive Comparison
Choosing the right VPN solution hinges on your unique requirements and platform. For Windows users, look for easy navigation, quick performance, and rigorous encryption. MacOS devotees should prioritize flawless operation with Apple ecosystems, while open-source advocates may favor configurable options.
Android and iOS users must opt for VPNs with compact software that limit energy usage and network load. Cross-platform compatibility is key if you regularly move between desktops, tablets, and devices. Always check that your VPN works with modern standards like IKEv2 for best results.
Step-by-Step Guide to Setting Up a VPN on PC Systems
First, navigate to the provider’s portal using a secure browser. Identify the installation page and select the PC-friendly edition. After acquiring the file, launch the executable and follow the installation wizard.
During setup, adjust settings like launch on boot and protocol selection. Activate the kill switch feature to halt exposure if the VPN disconnects. Lastly, authenticate with your account details and join a node of your choice.
Optimizing VPN Usage on MacOS
Mac systems delivers built-in compatibility for VPNs, but third-party apps often provide superior functionality. Post-installation, place the VPN software to your Applications folder. Open the app and key in your account information to initiate the service.
Customize settings such as protocol selection and geographical preferences. Turn on traffic filtering to route specific apps through the 快连电脑版 while letting others to use your standard internet. For extra security, combine your VPN with Firewall tools to prevent spyware and fraudulent links.
Securing Open-Source Platforms with a VPN
Tech enthusiasts often favor VPNs that accommodate command-line interfaces. First, upgrading your package manager to confirm access to the latest VPN software. Use CLI instructions to deploy the VPN application, adhering to guides provided by your provider.
Adjust network settings to automate VPN sessions during boot-up. Tech-savvy professionals can incorporate firewall rules to limit insecure connections. Regularly check records to detect irregularities and update your VPN software to fix weaknesses.
Protecting Handheld Gadgets with VPNs on Google’s OS and Apple’s Platform
Mobile devices are prime targets for data breaches due to their always-online nature. Download your VPN app from the Google Play Store to avoid copyright tools. Launch the app, sign in, and choose a server close to your region for faster speeds.
Enable tools including ad-blocking to boost your browsing experience. Set up the VPN to automatically link when accessing open hotspots. For iPhone owners, turn on continuous protection in device settings to maintain encryption even if the app terminates.
Advanced VPN Features to Boost Your Privacy
Modern VPNs provide premium functionalities that surpass standard protection. A emergency stop terminates all internet traffic if the VPN fails, blocking data exposure. Multi-hop directs your connection through two or more locations, obscuring your digital trail to a greater extent.
Threat detection systems eliminate annoying pop-ups and prevent phishing sites. Traffic division lets you select which apps use the VPN, optimizing performance and protection. For businesses, fixed locations and account control streamline encrypted communication.
Addressing Common False Beliefs About VPNs
Even with their adoption, many users misinterpret how VPNs function. A common fallacy is that VPNs fully anonymize your internet usage. While they hide your IP address, tracking cookies can still reveal your details. Additionally, few VPNs adhere to zero-data retention rules, so researching your provider’s practices is vital.
Another myth is that VPNs dramatically reduce connection rates. While security measures introduces delay, premium services reduce this impact with high-speed networks. Lastly, no-cost services often compromise privacy by monetizing user data or displaying targeted advertisements.
Future-Proofing Your Internet Activity with a VPN
As cyber threats advance, staying protected requires forward-thinking steps. Emerging trends like advanced algorithms could threaten current protection methods, making it crucial to opt for VPNs committed to enhancing their infrastructure. Integrating a VPN with supplementary measures click here like secure storage and biometric checks builds a comprehensive security strategy.
Regulators worldwide are tightening online protection statutes, and a VPN helps you comply with these rules. Whether you’re streaming content, gaming online, or managing work, a VPN remains an essential tool for operating the online realm securely.
 Michael Bower Then & Now!
Michael Bower Then & Now! Brandy Then & Now!
Brandy Then & Now!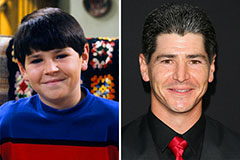 Michael Fishman Then & Now!
Michael Fishman Then & Now! Marcus Jordan Then & Now!
Marcus Jordan Then & Now! Daryl Hannah Then & Now!
Daryl Hannah Then & Now!